5.3 Smart cards and HSMs ¶
In this section we present the smart-card and hardware security module (HSM) support in GnuTLS using PKCS #11 [PKCS11]. Hardware security modules and smart cards provide a way to store private keys and perform operations on them without exposing them. This decouples cryptographic keys from the applications that use them and provide an additional security layer against cryptographic key extraction. Since this can also be achieved in software components such as in Gnome keyring, we will use the term security module to describe any cryptographic key separation subsystem.
PKCS #11 is plugin API allowing applications to access cryptographic
operations on a security module, as well as to objects residing on it. PKCS
#11 modules exist for hardware tokens such as smart cards9,
cryptographic tokens, as well as for software modules like Gnome Keyring.
The objects residing on a security module may be certificates, public keys,
private keys or secret keys. Of those certificates and public/private key
pairs can be used with GnuTLS. PKCS #11’s main advantage is that
it allows operations on private key objects such as decryption
and signing without exposing the key. In GnuTLS the PKCS #11 functionality is
available in gnutls/pkcs11.h.
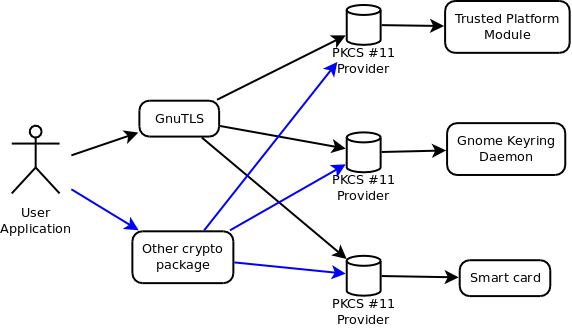
Figure 5.1: PKCS #11 module usage.